Welcome to SecretZero™¶
The Problem¶
If you have ever asked any of these questions about a new or existing git project then SecretZero is for you!
- Where are all the secrets in my project?
- How do I generate new secrets, api keys, or certificates to deploy a whole new environment?
- How do I handle secret-zero?
- When were my critical project secrets last rotated?
- If I needed to bootstrap this entire project from scratch would I be able to do so without manually handling any secrets?
- How do I document my project's secrets surface area and requirements?
Secrets Orchestration, Lifecycle, and Bootstrap Engine¶
SecretZero is a secrets management tool that automates the creation, seeding, and lifecycle management of project secrets through a declarative, schema-driven workflow. Think of it as:
- Terraform for secrets lifecycle - Declarative configuration for all your secrets
- Renovate for credentials - Automated rotation and lifecycle management
- npm/yarn for secret dependencies - Dependency graph and lockfile tracking
- A compliance tool - Built-in policies for SOC2, ISO27001, and custom requirements
🔒 Local-First Discovery
The discover command uses local AI models (Ollama) by default. No sensitive project data is sent to external services. All secret analysis happens on your machine. Optional remote LLM providers (OpenAI, Anthropic) require explicit configuration.
Active Development
SecretZero is actively being developed. Features and APIs may change between releases. Please refer to the CHANGELOG for breaking changes and version your dependencies accordingly.
Agent Quick Start¶
If you are an agent reading this project remotely through gh, curl, or a GitHub/MCP client,
start here.
Agent runtime integration (Hermes / OpenClaw):
export SZ_AGENT_MODE=true
secretzero agent list --format json
secretzero agent adopt --dry-run --format json
secretzero agent adopt --preseed-lockfile --format json
See skills/secretzero-agent-adopt/SKILL.md. secretzero agent backup is an alias of agent adopt
(not secretzero backup create).
Skill files:
https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-agent-adopt/SKILL.mdhttps://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-agent/SKILL.mdhttps://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-author/SKILL.mdhttps://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-handle/SKILL.md
Download all skill folders into a target directory:
curl -fsSL https://raw.githubusercontent.com/zloeber/SecretZero/main/scripts/download-secretzero-skills.zsh \
| bash -s -- ./skills
Use that downloader like this:
- OpenClaw: download to
./skillsfor the current workspace or~/.agents/skillsfor a shared install. - Hermes: either install the raw
SKILL.mdURLs withhermes skills install ..., or download to~/.agents/skills(or another shared directory) and add that directory to~/.hermes/config.yamlunderskills.external_dirs.
Direct Hermes install:
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-agent-adopt/SKILL.md
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-agent/SKILL.md
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-author/SKILL.md
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-handle/SKILL.md
Why SecretZero?¶
The Problem¶
If you've ever asked any of these questions about a codebase, SecretZero is for you:
- Where are all the secrets in my project?
- How do I generate new secrets to deploy a whole new environment?
- How do I handle secret-zero bootstrap?
- When were my critical project secrets last rotated?
- Can I bootstrap this entire project from scratch without manually handling secrets?
- How do I document my project's secrets surface area and requirements?
The Solution¶
SecretZero provides a single source of truth for all secrets in your project through a declarative Secretfile.yml:
version: "1.0"
metadata:
name: my-project
description: Production secrets configuration
secrets:
database_password:
template:
type: password
fields:
- name: value
generator:
type: random-password
length: 32
targets:
- type: aws-secretsmanager
name: /prod/db/password
- type: local-file
path: .env
format: dotenv
Key Features¶
🚀 Core Capabilities¶
- Idempotent Bootstrap - Generate initial secrets for one or more environments
- Lockfile Tracking - SHA-256 hashing with rotation history and timestamps
- Dual-Purpose Providers - Request/rotate secrets and store them across platforms
- Type Safety - Strongly-typed Pydantic models at every layer
- Multiple Profiles - Target multiple environments independently
- Environment Fallbacks - Manual secret override via environment variables
- Self-Documenting - Secrets-as-code showing provenance and distribution
🤖 AI-Powered Secret Discovery¶
- Automated Discovery - Find existing secrets, credentials, and sensitive configuration
- Local-First Analysis - All analysis runs locally using Ollama (no data leaves your machine)
- AI-Assisted - Uses language models to intelligently identify secret patterns
- Confidence Scoring - Distinguishes high-confidence from low-confidence discoveries
- Secretfile Generation - Auto-generates
Secretfile.detect.ymlwith recommendations - Privacy-Focused - Optional remote LLM support with explicit configuration required
🔄 Secret Rotation¶
- Secret Rotation - Policy-based rotation (90d, 2w, custom periods)
- Rotation Tracking - History, count, and timestamps in lockfile
- One-Time Secrets - Support for secrets that should never rotate
- Compliance Policies - Built-in SOC2 and ISO27001 support
🌐 API Service¶
- REST API - FastAPI-based HTTP API for programmatic management
- OpenAPI Docs - Interactive Swagger UI and ReDoc
- Secure Authentication - API key-based with timing-safe comparison
- Audit Logging - Comprehensive audit trail for all operations
- Remote Management - Manage secrets from CI/CD, scripts, or applications
☁️ Platform Support¶
- AWS - Secrets Manager, SSM Parameter Store, IAM roles
- Azure - Key Vault, Managed Identity
- HashiCorp Vault - KV v2, Token/AppRole auth
- GitHub - Actions secrets (repo, environment, org)
- GitLab - CI/CD variables (project, group)
- Jenkins - Credentials (string, username/password)
- Kubernetes - Secrets (all types), External Secrets Operator
- Native support for TLS, Docker registry, SSH keys
- Files - .env, JSON, YAML, TOML formats
- Merge/append support for existing files
Quick Start¶
Discover Existing Secrets¶
# Discover secrets using local AI analysis (Ollama required)
secretzero discover
# Reviews discovered secrets in Secretfile.detect.yml
# All analysis is local - no data leaves your machine
Installation¶
# Basic installation
uv tool install secretzero
# With cloud providers
uv tool install secretzero[aws,azure,vault]
# With CI/CD support
uv tool install secretzero[cicd]
# With API server
uv tool install secretzero[api]
# Everything
uv tool install secretzero[all]
Agent Skills¶
SecretZero also ships three focused agent skills:
secretzero-agentfor runtime bootstrap,agent sync, and secure operator handoffsecretzero-authorforSecretfile.ymlauthoring, review, and safe discovery workflowssecretzero-handlefor.env/ file-target workflows,SZ_AGENT_MODE, and spill-safe CLI usage
For the fastest remote install path, see Agent Quick Start near the top of this page.
If you are a human operator, install the CLI and use those skills as operating guides:
If you are running Hermes Agent, install the skills directly from this repository:
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-agent-adopt/SKILL.md
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-agent/SKILL.md
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-author/SKILL.md
hermes skills install https://raw.githubusercontent.com/zloeber/SecretZero/main/skills/secretzero-handle/SKILL.md
hermes skills list
If you already have a local checkout, you can also add the repo skill directory to ~/.hermes/config.yaml:
If you are running OpenClaw, opening this repository as the agent workspace is enough because OpenClaw auto-loads workspace /skills. To make the skills available across workspaces, copy them into ~/.agents/skills:
mkdir -p ~/.agents/skills
cp -R skills/secretzero-agent ~/.agents/skills/
cp -R skills/secretzero-author ~/.agents/skills/
cp -R skills/secretzero-handle ~/.agents/skills/
Or use the bundled downloader script from a remote agent session:
curl -fsSL https://raw.githubusercontent.com/zloeber/SecretZero/main/scripts/download-secretzero-skills.zsh \
| bash -s -- ~/.agents/skills
Initialize a Project¶
# Create a new Secretfile (or use discovered Secretfile.detect.yml)
secretzero create
# Validate configuration
secretzero validate
# Test provider connectivity
secretzero test
Generate and Sync Secrets¶
# Preview what would be generated
secretzero sync --dry-run
# Generate and sync secrets to all targets
secretzero sync
# Show status of a specific secret
secretzero show database_password
Manage Secret Lifecycle¶
# Check which secrets need rotation
secretzero rotate --dry-run
# Rotate secrets based on policies
secretzero rotate
# Check policy compliance
secretzero policy
# Detect drift from expected state
secretzero drift
Start the API Server¶
# Start the REST API server
export SECRETZERO_API_KEY=$(python -c "import secrets; print(secrets.token_urlsafe(32))")
secretzero-api
# Access interactive docs at http://localhost:8000/docs
Use Cases¶
-
Local Development
Generate development secrets locally with .env file support
-
GitHub Actions
Automated secret management for GitHub Actions workflows
-
Kubernetes
Native Kubernetes secret management and External Secrets Operator
-
Multi-Cloud
Synchronize secrets across AWS, Azure, and HashiCorp Vault
-
Compliance
SOC2 and ISO27001 compliance with policy enforcement
-
Augmenting
Augment your existing secret management tools
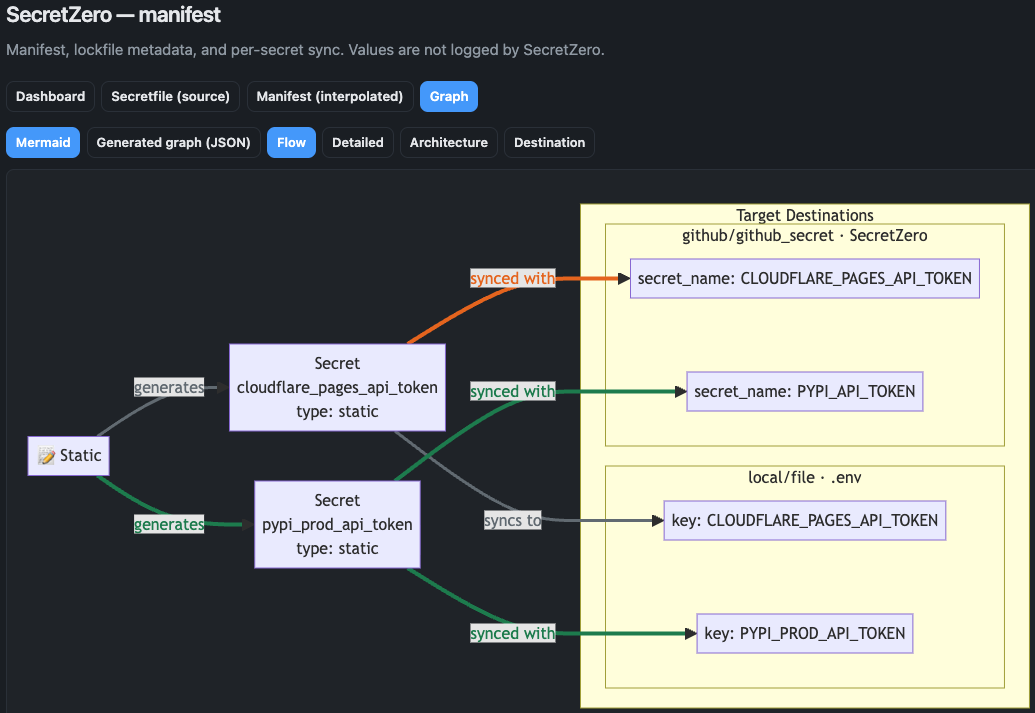
Workflow Visuals¶
See graph and sync workflow screenshots in the docs:
Architecture¶
SecretZero follows a clean, modular architecture:
graph TB
A[Secretfile.yml] --> B[Config Loader]
B --> C[Validation]
C --> D{CLI / API}
D --> E[Providers]
D --> F[Generators]
D --> G[Targets]
E --> H[Secret Sources]
F --> I[Secret Values]
G --> J[Storage Locations]
H --> K[Lockfile]
I --> K
J --> K
K --> L[.gitsecrets.lock]What's Next?¶
-
Get Started
Follow our step-by-step guide to set up your first project
-
User Guide
Learn about configuration, providers, targets, and CLI commands
-
Examples
Explore complete examples for different use cases
-
API Reference
Integrate SecretZero into your applications and workflows
Community¶
- GitHub: zloeber/SecretZero
- Issues: Report bugs or request features
- Discussions: Ask questions and share ideas
License¶
SecretZero is licensed under the Apache License 2.0.




